Post Compromise Active Directory Checklist
Nuke it from orbit, it’s the only way to be sure!
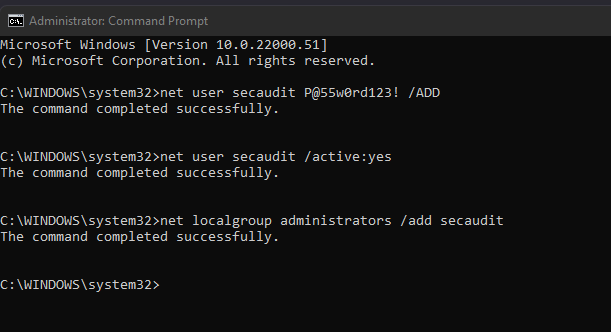
Ok, in an ideal world you can re-deploy your entire environment from scratch, but back in the most people’s real world’s that’s not that simple. So, what do we do if we can’t nuke from orbit in a post compromise situation? Well, we need to clean up! This isn’t an exhaustive list, not a total guide. it’s a quick list to make you think about some key common areas and actions that might need to be taken! after all if someone got r00t, who knows what they did! (trust me, most orgs monitoring is a bit naff!)
Read more “Post Compromise Active Directory Checklist”